Whereas, there are calls to “educate” the public on the alleged evils of Republic Act 10175 or the Philippine Cybercrime Prevention Act of 2012, it seems those who are making the loudest of such calls are themselves spreading information that may instead mis-educate the public.
 One Twitter user who goes by the name @BishopLuc posted a tweet stating implicitly as fact that the RA 10175 will in effect have legalised monitoring of ‘suspected individuals’. This was then retweeted by popular blogger Noemi Dado to her more than 11,000 followers. Pressed for clarification on what part of RA 10175 this assertion was based, @BishopLuc cited Section 12 of RA 10175 which reads…
One Twitter user who goes by the name @BishopLuc posted a tweet stating implicitly as fact that the RA 10175 will in effect have legalised monitoring of ‘suspected individuals’. This was then retweeted by popular blogger Noemi Dado to her more than 11,000 followers. Pressed for clarification on what part of RA 10175 this assertion was based, @BishopLuc cited Section 12 of RA 10175 which reads…
SEC. 12. Real-Time Collection of Traffic Data. — Law enforcement authorities, with due cause, shall be authorized to collect or record by technical or electronic means traffic data in real-time associated with specified communications transmitted by means of a computer system.
Traffic data refer only to the communication’s origin, destination, route, time, date, size, duration, or type of underlying service, but not content, nor identities.
All other data to be collected or seized or disclosed will require a court warrant.
Service providers are required to cooperate and assist law enforcement authorities in the collection or recording of the above-stated information.
The court warrant required under this section shall only be issued or granted upon written application and the examination under oath or affirmation of the applicant and the witnesses he may produce and the showing: (1) that there are reasonable grounds to believe that any of the crimes enumerated hereinabove has been committed, or is being committed, or is about to be committed: (2) that there are reasonable grounds to believe that evidence that will be obtained is essential to the conviction of any person for, or to the solution of, or to the prevention of, any such crimes; and (3) that there are no other means readily available for obtaining such evidence.
The second paragraph of Section 12 clearly stipulates that no content or identities will be part of data collected by law enforcement agencies from service providers where no court order is served for that purpose. And where such a court order is to be issued, three conditions need to be met first.
| SUPPORT INDEPENDENT SOCIAL COMMENTARY! Subscribe to our Substack community GRP Insider to receive by email our in-depth free weekly newsletter. Subscribe to our Substack newsletter, GRP Insider! Learn more |
Funny enough, @BishopLuc carried on and provided further “evidence” that the law is already being “abused” by the authorities. In a subsequent tweet, @BishopLuc cited as “evidence” an image uploaded to Facebook which had been going viral recently. The image supposedly captures comments made through a Facebook account operated by the Philippine National Police (PNP) warning people of the new powers and facilities the PNP will be wielding to apprehend users who use “foul words” against police officers.
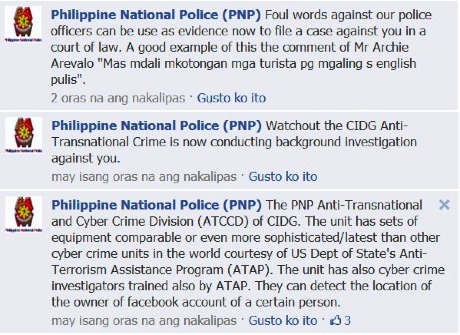
On account of this “evidence” of the PNP’s “abuse” of the new Cybercrime Prevention Law being just a digital image, there is no way to determine whether the messages shown in it are authentic. The PNP recently denied posting such remarks on Facebook and clarified the official channels through which it disseminates official PNP communication to the public.
“The PNP categorically denies any official connection to a message which appeared in one particular Facebook account found by many to be offensive, threatening and malicious,” [PNP spokesman Chief Superintendent Generoso Cerbo Jr] said.
He noted PNP official statements such as press releases intended for public consumption are published in digital form through the official PNP website or Facebook under the account name pnp.pio.
“Further, said official statements can be released individually to our media friend both in hard and digital copies in the name of the PNP Public Information Office,” he said.
The irony that seems to fly over the heads of our would-be online “activists” is that it is precisely this sort of thing — passing off unverified information as fact and propagating unfounded or hearsay information — that measures such as the sections relating to libel within RA 10175, however supposedly flawed this law is purported to be, seeks to mitigate.
Even otherwise highly-educated lawmakers are not above making use of such fear-mongering tactics. Earlier, Senator Teofisto Guingona III reportedly claimed that “If you click like [on Facebook], you can be sued, and if you share, and continuously re-share information, you can also be sued.” Not surprisingly, this factoid also spread like wildfire across the social media landscape.
At the core of such fears is the notion that the advent of RA 10175 spells the end of “free speech” in the Philippines. It is around this notion that calls to “action” are being incited. The tagline of a group that calls itself the Philippine Internet Freedom Alliance (PIFA), for example, is “stop cyber martial law”. As of this writing a rally before the Philippine Supreme Court is being organised for Tuesday, the 2nd of October. The following is an excerpt from the preamble supposedly guiding this mass movement:
The Cybercrime Prevention Act of 2012 or Republic Act No. 10175 threatens our basic rights and freedoms. This law works against ordinary netizens — bloggers, freelance writers, website owners, social network users. etc. — and disregards, among other things, our right to privacy and freedom of expression.
To safeguard these rights and freedoms, we, the members of the Philippine Internet Freedom Alliance (PIFA), ask you to leave the virtual world for a while, and join BLACK TUESDAY, a SILENT and PEACEFUL PROTEST against CYBER MARTIAL LAW.
Perhaps, rather than make such preambles required reading, people who are self-described advocates of freedom of information should, instead, encourage people to refer to reliable information on the subject and do their homework. Usually it helps to read what remains the most authoritative guide to the subject of Cybercrime prevention in the Philippines — none other than Republic Act 10175 itself which can be accessed here.
- The Philippine Senate has become a serious liability to the Filipino people and needs to be trashed ASAP! - May 28, 2026
- The Philippines’ outsourced justice system: why not outsource its executive and legislative branches too? - May 24, 2026
- Why are the Philippines’ “thought leaders” STILL so shocked that their “senate” is going down the shithole? - May 20, 2026
The screenshot about the “abuse” is, as far as I know, authentic since I saw it myself not as a screenshot but an actual post.
The problem is that the page is not an official page by PNP, and they pointed this out by showing how their site has always been pointing to the Facebook profile page pnp.pio. I verified this by accessing archives.org.
It could be worth noting that there is this “chain message” being spread by Filipino netizens via Facebook that reads:
“Warning -any person and/or institution and/or Agent and/or Agency of any governmental structure including but not limited to the United States Federal Government also using or monitoring/using this website or any of its associated websites, you do NOT have my permission to utilize any of my profile information nor any of the content contained herein including, but not limited to my photos, and/or…the comments made about my photos or any other “picture” art posted on my profile. You are hereby notified that you are strictly prohibited from disclosing, copying, distributing, disseminating, or taking any other action against me with regard to this profile and the contents herein. The foregoing prohibitions also apply to your employee, agent, student or any personnel under your direction or control the contents of this profile are private and legally privileged and confidential information, and the violation of my personal privacy is punishable by law. UCC 1-103 1-308 ALL RIGHTS RESERVED WITHOUT PREJUDICE
Please feel free to copy and use this post.For those of you who do not understand the reasoning behind this posting, Facebook is now a publicly traded entity. Unless you state otherwise, anyone can infringe on your right to privacy once you post to this site. It is recommended that you and other members post a similar notice as this, or you may copy and paste this version. If you do not post such a statement once, then you are indirectly allowing public use of items such as your photos and the information contained in your status updates.”
The aforementioned message has been already considered hoax a few months ago by Snopes, an well-known website about urban legends: http://www.snopes.com/computer/facebook/privacy.asp
Indeed, people are getting crazier by the minute regarding this issue!
Inquirer-dot quotes deLima when she says for all Not-To-Worry about the CyberCrime Law because she Will Always Be Respectful of the Constitution. She didn’t say if Senator Sotto will also Be-Respectful and Tolerant. And she didn’t say what Dept-Justice will do next yeaar or when that that next time happens and Malakanyang invokes POLICE-POWERS because one more time, PresiNoynoy hears voices calling him to action.
To collect data on peoples’ activities in the internet is a Violation of their Privacy, already. Why do Police collect data and activities on internet Bloggers?
It is Patriotic for every Filipino, not to follow the CyberCrime Law. It is against their Freedom of Expression, and Freedom of Speech. Do not cooperate with any Police in giving data, activities , etc. of people who are Blogging in the internet. You don’t want to give them Ropes to hang you…do you?
Why do Police collect data and activities on internet Bloggers?
Because there is a case against them.
Do not cooperate with any Police in giving data, activities , etc. of people who are Blogging in the internet.
lol. As if you are in control of that.
I am seeing other posts such as below. I am not a legal expert. Do they have a point?
1. Should libel be a civil case and not a criminal one?
2. Is the longer penalty in Republic Act 10175 compared to REvised Penal Code justifiable?
Use of the term “cyber martial law” is a form of the same sort of demagoguery that we criticise politicians for being guilty of — use of oversimplifications, loaded terminology, and no-sense symbolism to create reptilian emotional responses to what are really complex issues that require thinking.
The proof of the pudding is in the eating.
Until a case is filed against somebody for committing cyberspace libel we’ll never know what really are the actual implication of the new law.
Right now, there is an on-going frenzy and confusion as well as suspicion as to what would be the unforeseen ramifications of the recently approved law against social media netizens, in particular, and the overall state of cyberspace in general.
Ang cybercrime law ay matagal na sa ibang bansa. Huling huli na
tayo sa Pilipinas
nagkaroon ngbatas na
ito. Yong mga hackers na nagagalit sa batas na
ito ay mga criminal na
dapat parusahan. Dapat nang magkaroon nito kasi yong mga criminal ay computer na ang gamit, hindi na baril.
jerrry, alam mo , tama ka. Basta alam mo yung ibig sabhin nang “totalitarian regime “.
Omg, you’re so hardcore! lol
Iba yung hackers sa libelo. Iba yung pornograpia sa libelo. At yung libelo mismo e kasalukuyang pinagtatalunan pa kung ano ba talaga ito at nararapat bang pairalin ito sa cyberspace.
Ang labo mo. At least sa ibang bansa meron pa ring freedom of speech. And since maraming tanga dito sa Pilipinas, they take criticism against the government as ‘libelous’.
Baka IKAW ata ang makasuhan since you’re keeping on your schemes thru your falsified and questionable comments. 😛
http://www.gov.ph/2012/09/12/republic-act-no-10175/
you should read up bro. it might save you from being jailed by the very same law you are trying to promote.
██████████████████ [á´„á´á´á´á´‡É´á´› ʙʟá´á´„ᴋᴇᴅ.] (ʀᴀ É´á´. 10175)
And so it begins….
Teka, sa Facebook lang ba iyan?
@Jerrry what we are concerned is just a portion of the cybercrime law particularly in section (4).
You can be charged with libel with what you just posted here Jerrry. LOL
The tyranny of a very repressive cyber-crime law(emphasis on libel)will be given a hearing by the highest court in the land. The DOJ and law enforcement should not preempt the Supreme Court on this.
Despite constitutional safeguards I fear for my relatives who are children and teenagers should the law be implemented. The brilliant and idealistic among them could be harassed or politically persecuted for their opinions, views and comments. The same could be said of senior citizens. Silencing people by jailing them, destroying their lives and future in exposing them to hardened criminals is not justice!
This is not a threat. The state should be forewarned that a tyrant law that subjects senior citizens, children and teenagers to criminal prosecution for libel standing on shaky constitutional and legal grounds will cause widespread unrest among the sovereign people.
Blood is blood. When people become restive because of gross injustice they can resort to constitutional means short of violence to correct grave state wrongs. When people begin to see the grave threat to individual liberties and are pushed to the wall they have the power to change the government.
para sa akin tama lang nag mag karoon tayo ng ganitong batas … hindi naman nawala ung freedom of expression natin.. masasabi mo parin naman ung gusto mong sabihin… ayon nga lang meron limitasyon… sa akin lang naman just think before you click…
E bakit may comment blocked? Care to explain that?
It’s ok if we are like Singapore. But we have the wrong culture and the wrong leaders to cope with that kind of law. Of course, the culture of mediocrity in the Philippines still exist.
@batang 641
A tyrant state law that gravely abuses human rights and freedoms is not absolute and is certainly subject to the limitations of checks and balances. If you are not aware of the implications of this law then do some research on the net.
Tyranny succeeds because people like you are not aware of your individual freedoms and rights. “Sheep” kneel to tyranny… not free men, women and children.
@batang 641 it just shows your being naive.
Mas pag aaksayahan pa ba nila ng oras yan kesa sa dinami dami ng krimen at katuwalian d2 sa pinas?
Benign0
Here’s the link to the report which “explores key trends and challenges to the right of all individuals to seek, receive and impart information and ideas of all kinds through the Internet.â€
http://www2.ohchr.org/english/bodies/hrcouncil/docs/17session/A.HRC.17.27_en.pdf
This is the 15 May 2011 United Nations Human Rights Council Report of the Special Rapporteur on the promotion and protection of the right to freedom, of opinion and expression, Frank La Rue.
And here’s the link to the 07 June 2011 issue of Time concerning the La Rue U.N. Report with this headline:
“United Nations Report Declares Internet Access a Human Rightâ€
http://techland.time.com/2011/06/07/united-nations-report-declares-internet-access-a-human-right/#ixzz288s6H0Tv
all you talk, all you talk, why not comply! wtf
Is this really something to worry about?
Has anyone here heard of creating an on-line ‘personality’? In the event someone accusses you of on-line ‘SLANDER’,are you going to admit you did it?Someone got a hold of your PC and used it while you were not there? Facebook/internet entries are not admissible in court for this reason,no one really knows who typed the message,do they?
NO TO MENTION any type of ‘ENCRYPTION’ that utilizes VPN services type technology.Hide My Ass,Viper,Hide My Net are just three of 100’s of on-line servers that ‘HIDE’ people on-line.
Do not curse the darkness,light a candle instead.
Ang masasabi ko lang po,hindi maganda to kasi pano kung may gumamit ng facebook mo na ibang tao at ginamit nya sa masama O NAG POST SYA NG ANO-ANO AT NAG COMMENT NG MASAMA LABAG SA KAPWA NYA na di alam ng may ari, ang mapaparusahan ung tunay na maari na wala syang alam sa pangyayari.
Screenshots are the equivalent of hearsay unless backed by reputable data logs and timestamps.
I used to work white hat security for major websites. We hate the term and find it repulsive, but for purposes of explaining what it is, most people call it “Paid Hacker” where we are hired and purposely find potential exploits and make recommendations in how to improve the system. To clarify, I am not a hacker, its more like a security guard making sure all the locks are in place for a client and point out weak areas.
Every piece of evidence must be logged with corresponding data.
Example:
1. Screenshot must include – full and complete description of image / Date with GMT and local time / screen capture software used with complete version / resolution / compression method / saved internally with the image UNEDITED and UNCROPPED.
2. Accompanying process logs of the computer used to create screenshot and detailed report of the page which should include:
a. Primary and DNS servers
b. IP address of site
c. Reverse DNS results
d. Complete trace route results
e. IP address of the computer both public and private that was used to create the screenshot.
d. Complete specifications of the computer used to create screenshot.
3. Complete and detailed description on how the process was done to replicate the issue. Must include all technical details INCLUDING number of keystrokes made and total time elapsed.
4. And if possible, obtain server side data from server hosts and DNS providers only within the specific timeframe of event.
—
As you can see, it is not easy to prove a Cybercrime offense beyond reasonable doubt.
I hope our country is up for the challenge as this is not an easy task.